On-Premise Messenger for Business: The Complete Guide to Self-Hosted Corporate Communication in 2026

Every year, the list of reasons to move corporate communication off third-party clouds gets longer. Tightening data protection regulations. High-profile breaches involving major SaaS platforms. Government mandates requiring data to remain within national borders. For enterprises operating in banking, healthcare, defense, and government sectors, the message is unmistakable: if you do not control where your data lives, you do not control your data at all.
This is precisely why the on-premise messenger has become one of the most sought-after categories in enterprise software. Unlike cloud-hosted tools that store conversations, files, and metadata on servers you do not own, a self-hosted messaging solution places the entire communication stack within your organization’s infrastructure. Every message, every call, every file remains under your direct control.
In this guide, we break down everything decision-makers need to know about on-premise messaging in 2026: the core advantages, the technical requirements, the security architecture that matters, and what to look for when choosing a platform for your organization.
What Is an On-Premise Messenger and How Does It Differ from Cloud Solutions?
An on-premise messenger is a corporate communication platform whose server infrastructure is deployed and operated entirely within an organization’s own data center, private cloud, or physically controlled environment. This stands in direct contrast to SaaS messaging tools where the vendor hosts the servers, manages the databases, and controls the encryption keys on behalf of the client.
The distinction is not purely technical. It has profound implications for data ownership, regulatory compliance, and operational independence. When a message is sent through a cloud-hosted platform, it traverses infrastructure owned by the vendor, often passing through multiple jurisdictions and being stored in data centers subject to foreign legal frameworks. The US CLOUD Act, for example, enables American law enforcement to compel US-based technology companies to hand over data regardless of where it is physically stored. For a European bank, a Middle Eastern government agency, or an Asian healthcare network, this represents an unacceptable risk.
With an on-premise deployment, these risks disappear entirely. The organization controls the physical servers, manages the software, holds the encryption keys, and defines every security policy. No third party can access, subpoena, or compromise the data without breaching the organization’s own security perimeter.
7 Reasons Enterprises Choose On-Premise Messaging Over Cloud Alternatives
1. Absolute Data Sovereignty
Data sovereignty means your organization, and only your organization, determines where data is stored, who can access it, and under which legal framework it operates. On-premise deployment is the only architecture that guarantees this completely. Cloud vendors can promise data residency in specific regions, but they cannot eliminate the legal mechanisms that allow foreign governments to demand access to data held by companies under their jurisdiction.
2. Regulatory Compliance Without Compromise
Data localization laws are proliferating globally. GDPR in Europe, PDPA in Southeast Asia, national cybersecurity frameworks in Qatar, Saudi Arabia, and Oman, sector-specific regulations like HIPAA in healthcare and PCI DSS in financial services — all of these create compliance obligations that are significantly easier to meet when data never leaves your own infrastructure. An on-premise messenger eliminates the need to negotiate data processing agreements with cloud vendors and removes the risk of vendor non-compliance.
3. Zero Third-Party Access to Communication Data
Even when SaaS providers claim end-to-end encryption, they typically retain some level of access to metadata, user activity logs, and system configuration data. With an on-premise deployment, the vendor has no access to any of this information after the initial installation. The organization’s IT team manages updates, configurations, and security policies independently.
4. Air-Gapped and Restricted Network Operation
For defense organizations, intelligence agencies, and critical infrastructure operators, the ability to run communication systems in air-gapped environments, completely disconnected from the public internet, is a non-negotiable requirement. Cloud-based tools simply cannot operate in this mode. On-premise messengers like Gem Team can be configured for autonomous operation without any external internet connectivity, including failover recovery from backup cores in case of main system failure.
5. Integration with Existing Security Infrastructure
Enterprise environments typically include Data Loss Prevention (DLP) systems, Security Information and Event Management (SIEM) platforms, identity and access management (IAM) solutions, and anti-spam filters. An on-premise messenger can integrate directly with all of these systems because it operates within the same network. Cloud tools often require complex proxy configurations, API gateways, or intermediate services to achieve similar integration, and the results are rarely as seamless or auditable.
6. Full Administrative Control Over User Lifecycle
When the messaging platform lives on your own servers, your IT team has unrestricted control over user provisioning, deprovisioning, access levels, device policies, and data retention. There are no vendor-imposed limitations on administrative granularity. You can prevent specific user groups from copying text, forwarding files, or taking screenshots. You can enforce different authentication requirements based on role, department, or security clearance level.
7. Elimination of Vendor Lock-In and Cloud Dependency
The 2025 AWS outage demonstrated what happens when critical business operations depend on a single cloud provider. Communication platforms, authentication flows, and collaboration tools went down simultaneously across thousands of organizations. On-premise deployment eliminates this single point of failure. Your communication infrastructure operates independently of any external provider’s availability, uptime guarantees, or pricing decisions.
Security Architecture: What a Production-Grade On-Premise Messenger Must Include
Not every self-hosted chat application qualifies as an enterprise-grade on-premise messenger. The difference lies in security architecture. A platform built for mission-critical corporate communication needs to incorporate multiple defense layers that work together as a unified system, not as bolted-on features.
End-to-End Encryption with mTLS
All traffic between clients and servers must be protected by TLS 1.3 with mutual authentication (mTLS). This ensures that both ends of every connection verify each other’s identity before exchanging data. Standard TLS only authenticates the server. mTLS goes further by requiring the client to present a valid certificate, preventing man-in-the-middle attacks and unauthorized device connections.
Adaptive Multi-Factor Authentication
Static authentication is no longer sufficient. A production-grade on-premise messenger should implement adaptive MFA that adjusts security requirements based on real-time risk assessment. Gem Team’s approach illustrates this well: a login from a familiar device at the office during working hours requires only a password, while a login from an unknown device at an unusual location triggers additional factors such as hardware token verification, biometric confirmation, or trusted device approval.
| Risk Level | Context | Required Authentication |
| Low | Familiar device, office network, business hours | Password only |
| Medium | New device within familiar location | Password + OTP or biometrics |
| High | Suspicious IP, unknown device, off-hours | Password + hardware token + biometrics |
Granular Access Control Policies
Enterprise communication requires more than simple read/write permissions. A proper on-premise messenger should allow administrators to control, at the policy level, whether users can copy message text, forward files to external contacts, take screenshots, download attachments, or access the platform from personal devices. These controls must be configurable per user, per group, per department, and per security classification.
Emergency Mode and Data Destruction
For organizations operating in high-risk environments, the ability to trigger automatic data destruction upon an alert signal is critical. This includes wiping message databases, encryption keys, and cached files across all connected devices simultaneously. Combined with autonomous operation capabilities and failover recovery from backup systems, these features ensure communication continuity even in crisis scenarios.
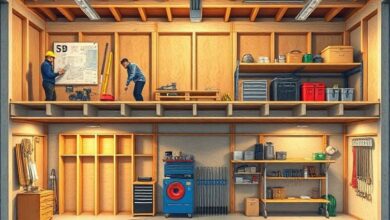
Implementing an On-Premise Messenger: A Step-by-Step Framework
Deploying a self-hosted messaging platform is a strategic project that requires careful planning. Here is the implementation framework that leading vendors, including Gem Team, follow to ensure successful deployments:
Step 1: Business Process Analysis and Solution DesignBegin with a comprehensive audit of your current communication landscape. Identify all official and unofficial messaging tools in use, map data flows, document compliance requirements, and define security policies. This analysis determines the optimal deployment architecture and configuration.
Step 2: Infrastructure Assessment and PlanningEvaluate your existing hardware and network infrastructure. A well-designed on-premise messenger should have low hardware requirements. Gem Team, for instance, requires a minimum processor frequency of just 2.4 GHz, making it deployable on existing enterprise hardware without significant capital investment.
Step 3: Product Demonstration and Stakeholder AlignmentBefore committing to a full deployment, conduct a proof-of-concept with key stakeholders from IT, security, compliance, and end-user departments. This validates that the platform meets all functional and regulatory requirements before scaling.
Step 4: Migration Planning and Data TransferDevelop a detailed migration plan covering email archives, chat histories, calendar data, and file repositories. A reliable vendor provides migration tools and hands-on assistance to ensure zero data loss during the transition.
Step 5: Deployment, Testing, and Security HardeningDeploy the platform, configure integration with existing security infrastructure (DLP, SIEM, IAM), conduct penetration testing, and validate all access control policies. Ensure emergency mode features function correctly if required.
Step 6: Training and Organizational OnboardingProvide comprehensive training for all user groups. The most common cause of enterprise messaging project failure is poor user adoption, which is almost always a training and change management problem rather than a technology problem.
Step 7: Ongoing Support and Continuous ImprovementEstablish a support framework with the vendor that includes regular security updates, performance monitoring, and proactive issue resolution. The platform should improve continuously based on organizational feedback and evolving threat intelligence.
On-Premise vs. Cloud vs. Hybrid: Detailed Comparison for Decision-Makers
The following comparison covers the most critical evaluation criteria that enterprise buyers should consider:
| Criterion | On-Premise | Cloud (SaaS) | Hybrid |
| Data Ownership | Complete — organization owns everything | Shared — vendor controls infrastructure | Split — based on architecture |
| Compliance Control | Direct — meets strictest regulations | Indirect — depends on vendor certs | Variable — per component |
| Air-Gap Capability | Yes | No | Partial |
| Third-Party Data Access | None | Possible (legal, technical) | Reduced |
| DLP/SIEM Integration | Native — same network | API-based — latency risk | Mixed |
| Initial Setup | Weeks to months | Hours to days | Weeks |
| Hardware Required | On-site servers (low specs OK) | None | Partial on-site |
| Vendor Dependency | Low (post-deployment) | High (ongoing) | Medium |
| Uptime Control | Internal SLA | Vendor SLA | Shared responsibility |
| Ideal For | Regulated industries, government | SMBs, startups, distributed teams | Large enterprises, multi-region |
Who Needs an On-Premise Messenger? Industry Use Cases
Banking and Financial Services
Financial regulators worldwide are cracking down on off-channel communication. The SEC, FCA, and MAS have all imposed significant fines on institutions whose employees conducted business through unapproved messaging tools. An on-premise messenger provides auditable, compliant communication records that reside entirely within the institution’s infrastructure, satisfying the most demanding regulatory requirements including PCI DSS, SOX, and national banking laws.
Government and National Security
Government agencies handling classified or sensitive information require communication systems that operate independently of commercial cloud infrastructure. The ability to deploy in air-gapped environments, support emergency data destruction protocols, and function without internet connectivity makes on-premise messaging essential for national security operations. Gem Team’s deployment experience with organizations aligned to Qatar’s National Vision 2030 and Oman’s Vision 2040 demonstrates the platform’s suitability for government-scale implementations.
Healthcare and Life Sciences
Patient data is among the most heavily regulated categories of information globally. HIPAA in the United States, GDPR in Europe, and national health data protection laws across Asia and the Middle East all impose strict requirements on where medical data can be stored, who can access it, and how it must be protected. An on-premise messenger ensures that clinical communication, patient records discussion, and care coordination all occur within a controlled environment that meets the most rigorous privacy standards.
Technology and Intellectual Property-Intensive Industries
Companies whose competitive advantage depends on trade secrets, proprietary algorithms, research data, or confidential client information cannot afford the risk of that information traversing third-party infrastructure. Self-hosted messaging ensures that intellectual property discussions remain within the corporate network, protected by the organization’s own security measures and not reliant on a vendor’s promises.
Evaluation Checklist: Choosing the Right On-Premise Messenger
Use this checklist when evaluating on-premise messaging platforms for your organization:
- Does the platform support true on-premise deployment on your own hardware, not just a private cloud hosted by the vendor?
- Does it use TLS 1.3 with mutual authentication (mTLS) for all traffic?
- Does it support adaptive multi-factor authentication with hardware tokens (FIDO2), biometrics, and OTP?
- Can administrators control text copying, file forwarding, screenshots, and downloads at the policy level?
- Can it operate in air-gapped mode without internet connectivity?
- Does it support automatic data destruction upon alert signals?
- Does it integrate natively with DLP, SIEM, and IAM systems?
- Does it offer video conferencing with recording, screen sharing, and large participant support?
- Does it include organizational directory features for onboarding and company structure navigation?
- Is it available across web, iOS, and Android with consistent security policies?
- What are the minimum hardware requirements? Can it run on existing infrastructure?
- Does the vendor provide migration tools and hands-on deployment support?
- Does the vendor have a proven track record with organizations in your industry and regulatory environment?
Frequently Asked Questions About On-Premise Messengers
What hardware is needed to run an on-premise messenger?
Requirements vary by platform and user count, but enterprise-ready solutions are designed to be efficient. Gem Team, for example, can run on hardware with a minimum processor frequency of 2.4 GHz. Most organizations can deploy on existing server infrastructure without purchasing dedicated hardware.
How long does on-premise deployment take?
A typical enterprise deployment takes between two and eight weeks, depending on the complexity of the environment, integration requirements, and data migration scope. The process includes analysis, demonstration, migration planning, deployment, testing, training, and go-live. Vendors with established deployment frameworks can accelerate this significantly.
Can an on-premise messenger be used by remote and mobile employees?
Yes. Modern on-premise messengers include native mobile applications for iOS and Android, as well as web-based access. Remote employees connect securely through the organization’s VPN or zero-trust network access (ZTNA) framework. The platform operates identically regardless of whether the user is in the office or working remotely.
Is it possible to switch from a cloud messenger to on-premise without losing data?
Yes, but it requires careful planning. Reputable on-premise messenger vendors provide dedicated migration tools and professional assistance to transfer email archives, chat histories, calendar data, and files. Gem Team includes secure migration capabilities as part of its deployment process, ensuring a smooth transition with minimal disruption to daily operations.
What happens if the on-premise server goes down?
Enterprise on-premise messengers include high-availability configurations and failover mechanisms. Gem Team supports failover recovery from backup cores in case of main system failure, ensuring communication continuity. Organizations can also implement redundant server configurations, automated backups, and disaster recovery procedures as part of their deployment architecture.
How does an on-premise messenger compare to Microsoft Teams in terms of features?
Leading on-premise messengers offer comparable collaboration features: instant messaging, group chats, video conferencing (Gem Team supports up to 300 participants), screen sharing, file sharing, channels, and organizational directories. The key differentiator is not features but architecture: on-premise platforms provide data sovereignty, air-gapped operation, and security controls that cloud-dependent tools like Microsoft Teams cannot match.
Conclusion: On-Premise Messaging Is the Foundation of Enterprise Communication Security
The decision to deploy an on-premise messenger is ultimately a decision about control. Control over where data lives. Control over who can access it. Control over how security policies are enforced. Control over whether your organization’s most sensitive conversations remain private or become vulnerable to foreign legal demands, vendor security failures, or cloud infrastructure outages.
In 2026, with data localization laws expanding across every major region, regulatory enforcement intensifying in financial services and healthcare, and geopolitical risks making cloud dependency increasingly problematic, the case for on-premise messaging has never been stronger. Organizations that make this investment now are not just solving today’s compliance challenges. They are building communication infrastructure that will serve them securely for years to come.
Gem Team, with seven years of platform development, proven deployments across government and enterprise sectors in the Gulf region, and a comprehensive feature set spanning encrypted messaging, video conferencing, and centralized administration, represents a mature and battle-tested option for organizations ready to take ownership of their corporate communications.
Published by: Gem Team Editorial | March 2026
Category: Enterprise Security, On-Premise Deployment, Corporate Communication
Tags: on-premise messenger, self-hosted messenger, enterprise communication, data sovereignty, zero trust, air-gapped messaging, Gem Team, secure corporate chat, DLP integration, adaptive MFA
Internal Links: gem.team/product/on-premise | gem.team/product/secure-business-messenger | gem.team/solutions/microsoft-teams-alternative